Protective Measures
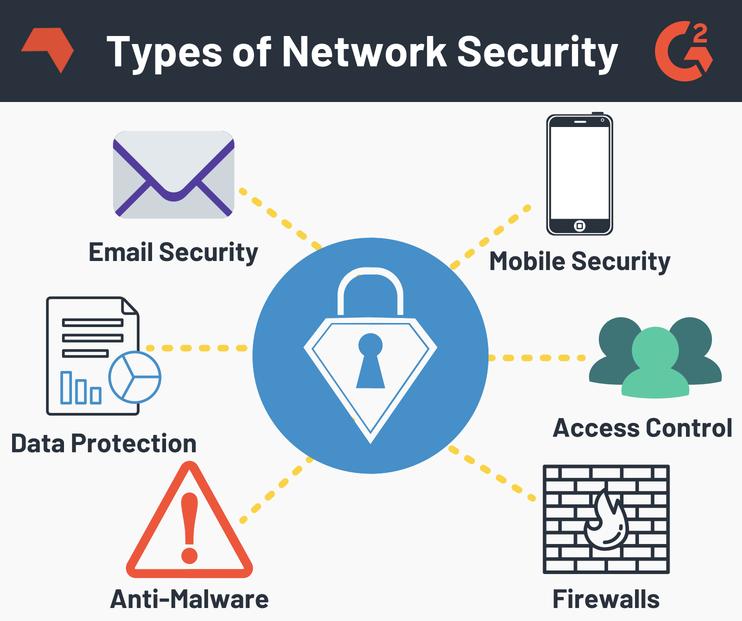
Access Control: Strict authentication and control of users accessing network resources. For example, perform user authentication, encryption, update, and authentication, setting permissions to access directory and files, etc., control network device configuration, and so on. Data encryption protection: Encryption is an important means of protecting data security. The role of encryption is to ensure that the information cannot be read after being intercepted.
Network Isolation Protection: There are two ways to isolate network isolation, one is implemented by an isolation card, one is implemented using a network security isolation gate gate.
Other measures: Other measures include information filtration, fault tolerance, data mirroring, data backup and auditing.
Preventive awareness
Having network security awareness is an important prerequisite for ensuring network security. Many network security incidents are related to lack of security awareness.
Security check
To ensure network security, network security construction, the first step must first fully understand the system, assess system security, recognize your risk, so rapid, Accurately solve the internal security problem.
Security Program
People sometimes I will forget the fundamental of security, just pursue new technologies for certain emotions, but found that it is finally worthless. In today's economic environment, limited security budgets can not allow the area where you have the highest risk of corporate risk to pursue what new technologies. Of course, these high-risk areas are not the same for all, and they will often change. Adverse molecules always make full use of these high-risk areas to implement attacks, and some of our very popular attacks today are not the type of attack we saw a few years ago. The purpose of writing this article is to see which security solutions can be covered to the most wide area to defend various new threats. From many ways, these solutions are all ideas that can be thought of without thinking, but you will be surprised to find that there are so many companies (whether big companies are still small businesses), they do not place them in place. The place. Many times they are just a placement.
The five basic security schemes given below, if combined, will effectively stop the data, networks, and users of the enterprise, will be combined than any five kinds of security technology in today's market. Good. Although there are many other very useful security solutions in the market, if you want to select 5 most effective and ready-to-use scenarios, then my choice is 5:
firewall < / b>
This piece of cornerstone of network defense has now been very needed for a solid foundation security. If there is no firewall shielding harmful flow, then the company will have an increase in the work of our network assets. The firewall must be deployed on the external boundaries of the enterprise, but it can also be placed inside the enterprise network to protect data security of each network segment. Deploying a firewall within an enterprise is still a relatively fresh but very good practice. This practice occurs mainly because any tangible network border that can distinguish between trusted traffic and harmful flow is disappearing. The concept of old so-called clear internet boundaries is no longer present in modern networks. The latest changes are that the firewall is becoming more intelligent, the particle size is fine, and it can be defined in the data stream. Today, the firewall controls the data stream based on a feature that applies types and even applications. For example, the firewall can block a SIP voice call according to the caller number.
Safety Router
(fw, ips, qos, vpn) - Routers are almost everywhere in most networks. According to conventions, they are only used as a traffic police that monitored traffic. But the modern router can do more than this. The router has a complete security feature, sometimes even more than the firewall. Today's most routers have a robust firewall function, and some useful IDS / IPS features, robust QoS and traffic management tools, of course, very powerful VPN data encryption. Such a function list can also list a lot. Modern routers are fully capable of increasing security for your network. Using modern VPN technology, it can be encrypted with all data streams on the enterprise WAN, but do not have to increase human hands. Some people can fully utilize some of its atypical purposes, such as firewall functions and IPS features. Open the router, you can see a lot of security conditions.
Wireless WPA2
The most organized one in this 5 major programs. If you haven't used WPA2 wireless security, please stop your security scheme and make a plan to prepare WPA2. Other many wireless security methods are not safe enough, and they can be cracked within minutes. So please use the WPA2 with AES encryption from today.
Email Security
We all know that the email is the most vulnerable object. Viruses, malware and worms like to use email as its communication channel. Email is the channel we are most likely to leak sensitive data. In addition to security threats and data loss, we will encounter unnealed spam in the email!
Web Security
Today, the threat from the 80-port and 443 ports are rapid than any other threat. In view of Web-based attacks, it is more complicated, so companies must deploy a robust Web security solution. Over the years, we have been filtered with a simple URL, which is indeed a core content of web security. However, Web security is far more than URL filtering is so simple, it also needs to be injected into av scan, malware scan, IP credit identification, dynamic URL classification skills and data leak prevention. The attackers are invading a lot of high-visa websites with amazing speed. If we only rely on the URL black and white list to filter, then we may only have the URL of the whitelist to access. Any Web security solution must be able to dynamically scan the web traffic to determine if the traffic is legal. In the five major security solutions listed here, web security is the cutting edge of security technology development, but also need to spend the most. Other solutions are most quite mature. Web security should go to fumet as soon as possible, return to real, and can resist the attacks initiated by hackers.
Security
According to network security status, and network security needs of enterprises in various fields, the security defense architecture of the entire network can be easily and easily. The security defense system of enterprise information systems can be divided into three levels: safety assessment, safe reinforcement, network security deployment.
Safety Assessment
Through the system security detection of enterprise network, Web script security detection, in a timely manner, in a timely manner, in a timely manner. For specific projects, a temporary project script code security audit team is established, and the security of the website programmer and the network security engineer are common to the security of the website program. Find out the presence of security hazard programs and prepare relevant remedies.
Safely reinforcement
Based on the detection result of the network security assessment, the vulnerability exists in the website application, the malicious code exists in the page is thoroughly cleared, and the website is related to the website. Safety source code audit, find out the source code problem, safe fix. Safety reinforcement is a proactive safety protection means, providing real-time protection for internal attacks, external attacks and misuse, intercepts and responding to intrusion before the network system is harmful, and strengthen the security of the system itself.
Network Security Deployment
In the enterprise information system, the deployment of secure products can be used to protect the network system to provide stronger security monitoring and defense capabilities.
