Login
Although the Telnet service is also a service of the client/server model, its greater significance lies in the realization of remote login (remote interactive computing) based on the Telnet protocol, then Let us know about remote login.
Definition
Let’s first take a look at what is login: The time-sharing system allows multiple users to use a computer at the same time. In order to ensure the security of the system and the convenience of accounting, the system requires each The user has a separate account as the login identification, and the system also assigns a password for each user. The user must enter the ID and password before using the system. This process is called'login'. Remote login refers to the process in which users use Telnet commands to temporarily make their computer an emulation terminal of the remote host. The emulation terminal is equivalent to a non-intelligent machine. It is only responsible for passing every character input by the user to the host, and then echoing every information output by the host on the screen.
Generation and development
We can first imagine a service that provides remote text editing. The realization of this service requires a server that accepts file editing requests and data and a client that sends this request. machine. The client will establish a TCP connection from the local machine to the server. Of course, this requires a response from the server, and then sends the typed information (file editing information) to the server, and reads the output returned from the server. The above is a standard and common client/server model service.
It seems that with the client/server model of service, all remote problems can be solved. However, the reality is not as simple as you think. If we only need to edit files remotely, then the service we just conceived can be adequate, but if our requirements are not so simple, we also want to realize remote user management, remote data entry, and remote System maintenance, if you want to achieve all the operations that can be implemented on the remote host, then we will need a large number of dedicated server programs and use a server process for each computable service. The problem that follows is: the remote machine will be very fast Overwhelmed by the server process, and submerged in a sea of processes (we exclude the most specialized remote machines here).
So is there a solution? Of course, we can use remote login to solve all this. We allow users to establish a login session on a remote machine, and then execute commands to achieve the same as local operations. In this way, we can access all available commands on the remote system, and the system designer does not need to provide multiple dedicated server programs.
The problem seems to have a bright future here. Using remote login should always solve the problem, but it is not easy to achieve remote login. Computer systems that do not consider network design expect users to log in only from directly connected keyboards and monitors. Adding remote login functions to such machines requires modifying the machine's operating system, which is extremely difficult and we try to avoid it. Therefore, we should focus on constructing remote login server software, although this is also more difficult. Why is it more difficult to do so?
For example: Generally, the operating system assigns special meanings to some special keys. For example, the local system interprets'Ctrl+C' as:'Terminate the currently running command process'. But suppose we have already run the remote login server software,'Ctrl+C' may not be transmitted to the remote machine, if the client really transmits'Ctrl+C' to the remote machine, then the'Ctrl+C' The command may not be able to terminate the local process, which means that confusion is likely to occur here. And this is just one of the problems encountered.
But despite the technical difficulties, system programmers managed to construct remote login server software that can be applied to most operating systems, and construct application software that acts as a client. Usually, the client software cancels the local interpretation of all keys except one key, and converts these local interpretations into remote interpretations accordingly. This makes the interaction between the client software and the remote machine just like sitting on the remote host The same as before, thus avoiding the confusion mentioned above. The only exception key can bring the user back to the local environment.
The remote login server is designed as application-level software, and there is another requirement, that is, the operating system needs to provide support for pseudoterminal (pseudoterminal). We use pseudo-terminals to describe the entry point of the operating system, which allows programs like Telnet servers to transfer characters to the operating system and makes the characters appear to come from a local keyboard. Only by using such an operating system, can the remote login server be designed as application-level software (such as Telnet server software), otherwise, the local operating system and remote system transmission will not be able to identify the information transmitted from the other side (because they can only identify the slave The information typed in the local keyboard), the remote login will fail.
Designing the remote login server as application-level software has its obvious advantages: it is easier to modify and control the server than embedding the code in the operating system. But it also has the shortcoming of low efficiency (the content will be explained later). Fortunately, the rate at which users type information is not high, so this design is still acceptable.
Working process
When using Telnet protocol to log in remotely, the following conditions must be met: a client program containing Telnet protocol must be installed on the local computer; the IP address of the remote host or Domain name; you must know the login ID and password.
Telnet remote login service is divided into the following 4 processes:
1) Establish a connection between the local and the remote host. The process is actually to establish a TCP connection, and the user must know the IP address or domain name of the remote host;
2) The user name and password entered on the local terminal and any commands or characters entered later are converted to NVT ( NetVirtualTerminal) format to the remote host. This process actually sends an IP data packet from the local host to the remote host;
3) Convert the data in NVT format output by the remote host into the format accepted by the local and send it back to the local terminal, including input commands Echo and command execution results;
4) Finally, the local terminal cancels the connection to the remote host. The process is to withdraw a TCP connection.
The above content only discusses the most basic things of remote login. The complexity and the hardship of programmers are unimaginable to us. I don't know if you think of these while using Telnet comfortably!
Function
Usage
Telnet is the standard protocol and main method of Internet remote login service. It was originally developed by ARPANET and is now mainly used for Internet sessions. The basic function is to allow users to log in to the remote host system.
Telnet allows us to sit in front of our computer and log in to another remote computer through the Internet. This computer can be in the next room or on the other side of the earth. After logging in to the remote computer, the local computer is equivalent to a terminal of the remote computer. We can directly manipulate the remote computer with our own computer and enjoy the same operating authority as the local terminal of the remote computer.
The main purpose of Telnet is to use the information resources on the remote computer that the local computer does not have. If the main purpose of the remote is to transfer files between the local computer and the remote computer, then FTP is used in comparison. Will be faster and more effective.
Interaction process
When we use Telnet to log in to the remote computer system, two programs are actually started: one is the Telnet client program, which runs on the local host; the other is Telnet server program, which runs on the remote computer to be logged in.
The Telnet client program on the local host mainly completes the following functions:
Establish a TCP connection with a remote server.
Receive locally typed characters from the keyboard.
The input string is converted into a standard format and sent to the remote server.
Receive the output information from the remote server.
Display this information on the screen of the local host.
The "service" program of the remote host is usually nicknamed the "elf". It usually waits silently on the remote host and receives a request from the local host. , It will immediately become active and complete the following functions:
Notify the local host that the remote host is ready.
Wait for the local host to input commands.
Respond to commands from the local host (such as displaying the contents of a directory, or executing a program, etc.).
Send the result of executing the command back to the local computer for display.
Wait for the command from the local host again.
In the Internet, many services adopt such a client/server structure. For the user, it is usually enough to understand the client's program.
Security hazards
Although Telnet is relatively simple, practical and convenient, Telnet is not reused in modern network technologies that pay special attention to security. The reason is that Telnet is a clear text transmission protocol, which transmits all user content, including user names and passwords, in clear text on the Internet, which poses certain security risks. Therefore, many servers choose to disable the Telnet service. If we want to use Telnet remote login, we should check and set the function of allowing Telnet service on the remote server before use.
Protocol
We know that Telnet server software is our most commonly used remote login server software. It is a typical client/server model service, which uses the Telnet protocol to work. So, what is the Telnet protocol? What characteristics does it have?
Basic content
Telnet is a protocol located on the 7th layer of the OSI model---the application layer. It is a protocol that provides terminal emulation for connecting to a remote host by creating a virtual terminal TCP/IP protocol. This protocol requires authentication through a user name and password, and is a standard protocol for Internet remote login services. The Telnet protocol can turn the computer used by the local user into a terminal of the remote host system. It provides three basic services:
1) Telnet defines a network virtual terminal to provide a standard interface for the remote system. Client programs do not need to know the remote system in detail, they only need to construct programs that use standard interfaces;
2) Telnet includes a mechanism that allows the client and server to negotiate options, and it also provides a set of standard options; .
3) Telnet handles both ends of the connection symmetrically, that is, Telnet does not force the client to input from the keyboard, nor does it force the client to display output on the screen.
Adapt to heterogeneous
In order to make Telnet interactive operation between multiple operating systems possible, it is necessary to have a detailed understanding of heterogeneous computers and operating systems. For example, some operating systems require each line of text to end with an ASCⅡ carriage return control character (CR), other systems require ASCⅡ line feed (LF), and some systems require a two-character sequence carriage return-line feed (CR). -LF); For another example, most operating systems provide users with a shortcut key to interrupt the running of the program, but this shortcut key may be different in each system (some systems use CTRL+C, while other systems use ESCAPE). If the heterogeneity between systems is not considered, the characters or commands issued locally are likely to be inaccurate or wrong after being transmitted to the remote place and interpreted by the remote system. Therefore, the Telnet protocol must solve this problem. In order to adapt to the heterogeneous environment, the Telnet protocol defines the transmission method of data and commands on the Internet. This definition is called the network virtual terminal NVT (NetVirtualTerminal). Its application process is as follows: For sent data: the client software converts the keystrokes and command sequences from the user terminal into NVT format and sends them to the server, and the server software converts the received data and commands from NVT format to remote locations. The format required by the system; for the returned data: the remote server converts the data from the remote machine format to the NVT format, and the local client converts the received NVT format data to the local format. For the detailed definition of NVT format, friends who are interested can find relevant information.
Transmit remote commands
We know that most operating systems provide various shortcut keys to implement corresponding control commands. When the user types these shortcut keys in the local terminal, the local The system will execute the corresponding control commands without using these shortcut keys as input. So for Telnet, what does it use to realize remote transmission of control commands? Telnet also uses NVT to define how to transfer control functions from the client to the server. We know that the ASCⅡ character set includes 95 printable characters and 33 control codes. When the user types a common character locally, the NVT will transmit it according to its original meaning; when the user types a shortcut key (combination key), the NVT will convert it into a special ASCⅡ character for transmission on the network, and then reach the remote machine Then converted into corresponding control commands.
The reason for distinguishing the normal ASCⅡ character set from the control command:
1) This distinction means that Telnet has greater flexibility: it can be transmitted between the client and the server All possible ASCⅡ characters and all control functions;
2) This distinction allows the client to specify the signaling without ambiguity, without causing confusion between control functions and ordinary characters. .
Data flow
As we mentioned above, there is a shortcoming of designing Telnet as application-level software, that is, it is not efficient. Why is this? The data flow in Telnet is given below:
Data information is typed in by the user from the local keyboard and passed to the client program through the operating system. The client program processes it and returns it to the operating system, and the operating system passes through it. Network transmissionSend the data to the remote machine, the remote operating system transmits the received data to the server program, and returns to the pseudo terminal entry point on the operating system after being processed again by the server program. Finally, the remote operating system transmits the data to the application program that the user is running. , This is a complete input process; the output will be transmitted from the server to the client according to the same path. Because of each input and output, the computer will switch the process environment several times, and this overhead is very expensive. Fortunately, the user's typing rate is not high, and we can still accept this shortcoming. .
Force Command
We should consider such a situation: Suppose that the local user runs an endless loop of wrong commands or programs on the remote machine, and this command or program It has stopped reading input, then the buffer of the operating system may be filled up. If so, the remote server can no longer write data to the pseudo terminal, and eventually stop reading data from the TCP connection, the buffer of the TCP connection Eventually it will be full, which will prevent data flow from flowing into this connection. If the above things happen, the local user will lose control of the remote machine.
In order to solve this problem, the Telnet protocol must use external signaling to force the server to read a control command. We know that TCP uses an emergency data mechanism to implement external data signaling, so Telnet only needs to attach a reserved octet called a datemark, and notify the server by letting TCP send a segment with emergency data bits set. That's it, the message segment carrying urgent data will bypass the flow control and reach the server directly. As a response to emergency signaling, the server will read and discard all data until it finds a data tag. The server will return to normal processing after encountering the data mark.
Because of the heterogeneity of the machines and operating systems at both ends of Telnet, it is impossible and should not strictly specify the detailed configuration of each telnet connection, otherwise it will greatly affect Telnet's adaptability to heterogeneity. Therefore, Telnet uses an option negotiation mechanism to solve this problem.
The range of Telnet options is very wide: some options expand the general direction of the function, and some option systems involve some minor details. For example: there is an option to control whether Telnet works in half-duplex or full-duplex mode (large direction); there is also an option to allow the server on the remote machine to determine the user terminal type (small details).
The negotiation method of Telnet options is also very interesting. It handles each option symmetrically, that is, either end can send out an application for negotiation; either end can accept or reject the application. In addition, if one end tries to negotiate an option that the other end does not understand, the end accepting the request can simply refuse the negotiation. Therefore, it is possible to interoperate newer, more complex Telnet client server versions with older, less complex versions. If both the client and the server understand the new options, the interaction may be improved. Otherwise, they will all switch to a less efficient but working mode to run. All these designs are to enhance the adaptation to heterogeneity, which shows how important Telnet is to its application and development.
Some principles are discussed above. Although it is difficult for us to touch this level in the use of Telnet, I think it is meaningful to understand these and it will bring us a lot of enlightenment. . Let's take a look at the Telnet service of Win2000.
Sub-option negotiation
Some options cannot be expressed simply by "activating" or "prohibiting". Specifying the terminal type is an example. The client process must send an ASCII string to indicate the terminal type. In order to deal with such options, we must define a sub-option negotiation mechanism.
RFC1091[VanBokkelen1989] defines how to express the sub-option negotiation mechanism of the terminal type. The first connected party (usually the client process) sends a 3-byte character sequence to request the activation of this option.
The 24 (decimal) here is the ID number of the terminal type option. If the receiving end (usually the server process) agrees, the response data is:
Then the server process sends the following string:
This string asks the terminal type of the client process. SB is the initial command flag for sub-option negotiation. The "24" in the next byte represents that this is a sub-option of the terminal type option (usually the option value after SB is the content to be submitted for the sub-option). The "1" in the next byte means "send your terminal type". The end command flag for sub-option negotiation is also IAC, just like SB is the start command flag. If the terminal type is ibmpc, the response command of the client process will be:
The 4th byte "0" represents "my terminal type is" (the AssignedNumbersRFC document has a formal value for the terminal type Definition, but at least between Unix systems, the terminal type can be represented by any data that the other party can understand. As long as these data are defined in the termcap or terminfo database). During the Telnet sub-option negotiation process, the terminal type is expressed in uppercase, and when the server receives the string, it will automatically be converted to lowercase characters.
Configuration
Actually from the application level, Win2000 Telnet service has nothing to say, most of the content can be obtained from the HELP file, I just put It just tidied up a bit. Win2000 provides us with Telnet client and server programs: Telnet.exe is the client program (Client), tlntsvr.exe is the server program (server), and it also provides us with the Telnet server management program tlntadmn.exe.
The Telnet service is installed by default in Windows 2000, but it is not started by default. The following is a part of the default settings of the Telnet service in the HELP file:
AllowTrustedDomain: Whether to allow domain users to access. The default value is 1, allowing users in trusted domains to access. It can be changed to 0: domain users are not allowed to access (only local users are allowed).
DefaultDomain: You can set any domain that has a trust relationship with the computer. The default value is ".".
DefaultShell: Display the path location of the shell installation. The default value is: %systemroot%\System32\Cmd.exe/q/k
MaxFailedLogins: Displays the maximum number of failed login attempts before the connection is terminated. The default is 3.
LoginScript: Display the path location of the Telnet server login script. The default location is "%systemroot%\System32\login.cmd". You can change the script content so that the welcome screen for logging into Telnet will be different.
NTLM: NTLM authentication option. The default is 2. Can have the following values:
0: Do not use NTLM authentication.
1: Try NTLM authentication first, if it fails, then use the username and password.
2: Only use NTLM authentication.
TelnetPort: Shows the port on which the telnet server listens to telnet requests. The default is: 23. You can also change to other ports.
You can use tlntadmn.exe (Telnet server management program) to configure the above settings very conveniently. After configuration, you need to restart the Telnet service.
NTLM
When you mention telnet, you have to mention NTLM. I think this is also the most troublesome thing for intruders. Even if you get the administrator account and password, think simple Passing NTLM is not easy, and telnet in win2000 only uses NTLM to verify identity by default, which makes us have to pay attention to NTLM, so what is NTLM?
The early SMB protocol transmits passwords in clear text on the network. Later, the "LANManagerChallenge/Response" authentication mechanism, or LM for short, appeared. It is very simple and easy to crack. Microsoft subsequently proposed WindowsNT challenge/response authentication. Mechanism, namely NTLM. Now there is an updated NTLMv2 and Kerberos authentication system.
Process
1. The client first encrypts the current user's password locally to become a password hash
2. The client sends its own account to the server. This account is not encrypted and is directly transmitted in plain text.
3. The server generates a 16-bit random number and sends it to the client as a challenge (question password; challenge)
4. The client then uses the encrypted password hash to encrypt the challenge, and then returns this to the server. As a response (response)
5. The server sends the three things of the user name, the challenge to the client, and the response returned by the client to the domain controller
6. The domain controller uses this username to find the user's password hash in the SAM password management database, and then uses this password hash to encrypt the challenge.
7. The domain controller compares the two encrypted challenges, and if they are the same, the authentication is successful.
From the above process, we can see that NTLM sends a login request to the Telnet server as the current user, instead of logging in with the account and password of the other’s administrator you scanned. Obviously, you Will fail to log in. For example, your home machine is named A (local machine), the machine you hacked is named B (remote machine), your account on A is xinxin, and the password is 1234, you scan to the management of B The user account is Administrator and the password is 5678. When you want to Telnet to B, NTLM will automatically use the current user’s account and password as the login credentials to perform the above 7 operations, that is, use xinxin and 1234 instead of scanning. The Administrator and 5678 that have arrived, and these are all done automatically, do not give you the opportunity to intervene at all, so your login operation will fail.
Display
Since the Telnet server has 3 options for NTLM use, when you Telnet a remote machine, one of the following situations will be displayed:
< p>1) When the authentication option=0========================= ===========
Microsoft(R)Windows(TM)Version5.00(Build2195)
WelcometoMicrosoftTelnetService
TelnetServerBuild5.00.99201 .1
login:
password:
When \ is 0, NTML authentication is not used, directly enter the user name and password, for example, you can enter the scanned Administrator and 5678
2) When authentication option=1
================== ===================
NTLMAuthenticationfailedduetoinsufficientcredentials.Pleaseloginwithcleartextusernameandpassword
Microsoft(R)Windows(TM)Version5.00(Build2195)
WelcometoMicrosoftTelnetService
TelnetServerBuild5.00.99201.1
login:
password:
\Try NTLM identity first Verification, if it fails, use the user name and password. In fact, for us, this method is no different from the previous method.
3) When the authentication option=2< /p>
=====================================
NTLMAuthenticationfailedduetoinsufficientcredentials.Pleaseloginwithcleartextusernameandpassword
ServerallowsNTLMauthenticationonly
Serverhasclosedconnection
Missing host Connection.
C:\
\Look at the above display carefully, there is no opportunity to enter your username and password at all, so you can disconnect directly and scan the password as a white scan
So for the intruder, NTLM is a mountain in front of us, we must get rid of it. Generally, we have the following methods:
1 Change the telnet by modifying the remote registry Server configuration, change the authentication mode from 2 to 1 or 0;
2 Use NTLM.exe, run directly after uploading, and change the telnet server authentication mode from 2 to 1;
3 Create a scanned user locally, open the telnet client as this user and log in remotely;
4 Use software, such as opentelnet.exe (administrator rights are required and the IPC channel is opened)
p>
5 Use scripts such as RTCS, (Requires administrator permissions but does not rely on IPC pipes)
Basically, the above 5 types, of which the latter two are our more commonly used methods to open telnet, and the method of use is very simple, the command is as follows:
OpenTelnet.exe\serverusernamepasswordNTLMAuthortelnetport
OpenTelnet.exe\server address administrator username password authentication method (fill in 0 or 1) telnet port
cscriptRTCS.vbetargetIPusernamepasswordNTLMAuthortelnetport
cscriptRTCS.vbe
Remote login
Telnet is used for remote login of the Internet. It can make the user sit on the Internet. In front of the computer keyboard, another computer that has accessed the Internet through the network connects them to each other. This connection can happen to computers in the same room or computers that have been online in all parts of the world. Traditionally, they are connected. The computer, and the computer that provides services for all users on the network is called the server (Server), and the machine you are using is called the client (Client). Once connected, the client can enjoy all the services provided by the server. Users can run the usual interactive process (register to enter, execute commands), and can also access many special servers such as searching for book indexes. Various services provided by different hosts on the Internet can be used.
Telnet
(telnet)(n.)AterminalemulationprogramforTCP/IPnetworkssuchastheInternet.TheTelnetprogramrunsonyourcomputerandconnectsyourPCtoaserveronthenetwork.YoucanthenentercommandsthroughtheTelnetprogramandtheywillbeexecutedasifyouwereenteringthemdirectlyontheserverconicate ssword.TelnetisacommonwaytoremotelycontrolWebservers.
Telnet command
The easiest way to use Telnet is to type in the command line:
%telnetremote-computer-name(orIP)< /p>
The Cshell of the UNⅨ system is used here, because the command selection is the percent sign "%". If you are using other computer systems (such as: Dos, VAX/VMS, Macintosh) commands, only There are some differences in the details, but the essence is similar. Here is a basic Telnet usage example:
telnetporky.math.
Trying129.237.128.11...
Connectedtoporky.math
Escapecharacteris'^]'.
SunOSUNⅨ(porky)
login:wl
password:xxxxxxx
LastLogin:TueMar2805:35fromns
SunOSRelease4.1.3_U1(SLIPPERY1)#3:SunNov2023:47:23CST1999
Nomatch.
if:Expressionsyntax.
porky/serv/wl%ls
hello
porky/serv/wl%
porky/serv/ wl%cd/
porky/%ls
Mail/dev/home/mnt/sbin/
usr/
News/ domain/home1/net/serv/
var/
Record/etc/kadb*pcfs/sys@
vmunix*
bin@export/lib@printtmp/
bootgofer/lost+found/recordtmp_mnt/
porky/%
The above example is to use Telnet to find one called porky .math's remote computer. After finding this computer, the user's computer that has been online becomes one of its terminals. At this time, the dialog that appears on the screen is the same as the terminal that the user connects on the host. The user must log in (login) and log out (logout). After logging in, any command suitable for the remote system can be given, because "for the UNⅨ system, all standard UNⅨ commands (like ls and pwd) can be used When the user exits from the remote system, he also exits from Telnet, and can run his own local system. In fact, Telnet is a tool that can be registered into the remote computer system.
Command
help online help
open followed by the IP address or domain name to log in remotely
close normally ends the remote session and returns to the command mode
display Display working parameters
mode enter the line command or character mode
send send special characters to the remote host (type send? to display detailed characters)
set set work Parameters (type set? to display detailed parameters)
status display status information
toggle to change working parameters (type toggle? to display detailed parameters)
^] Escape character (escapecharacter), exit the session under abnormal circumstances, and return to the command mode
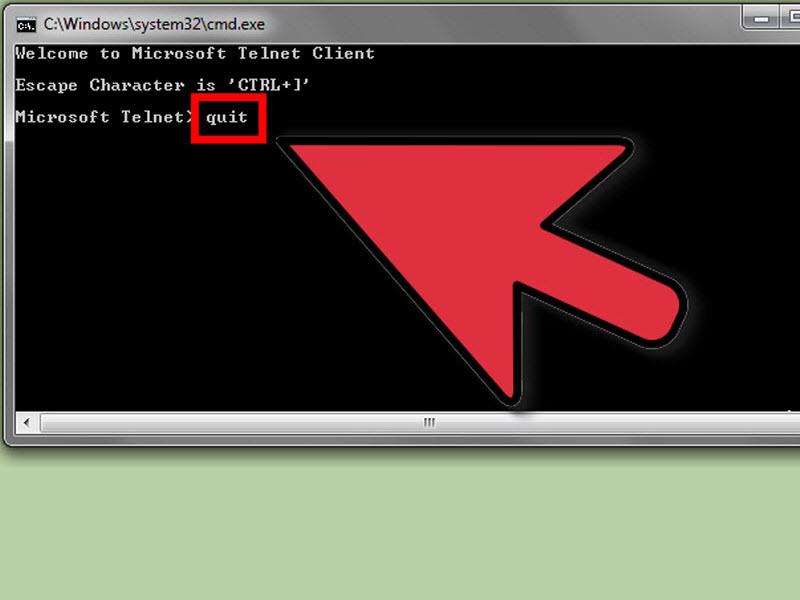
quit Quit telnet and return to the local machine
z make telnet enter the pause state
< p>; End the command mode and return to the telnet session modeSecurity issues of telnet.exe
It is recommended to modify permissions, delete all users and save only Administrators and SYSTEM as all permissions
p>Frequently Asked Questions
1. What is Telnet? Answer: Telnet is the abbreviation of teletypenetwork, which has now become a proper noun, indicating the remote login protocol and method, divided into Telnet client and Telnet Server program. Telnet allows users to remotely log in to the remote Telnet server on the local Telnet client.
2. What is the function of Telnet? Answer: Telnet provides remote login function, allowing users to be on the local host Run Telnet client, you can log in to the remote Telnet server. Commands entered locally can be run on the server, and the server will return the results to the local, just like operating directly on the server console. In this way, you can remotely operate and operate locally. Control server.
3. What are the Telnet working modes? Answer: There are four working modes for Telnet:
1) Half-duplex: The client must start from The server process gets the GOAHEAD(GA) command. It is rarely used now.
2) One at a time Characters: The client sends each character entered by the user to the server separately, and the server echoes the character back to the client. It is the default method of most Telnet programs. The SUPPRESSGOAHEAD option and the ECHO option must be valid at the same time.
3) Kludgeline mode (kludgelinemode): Each time the user enters a line of information, the client sends it to the server once. This mode is used when one of the above two options is invalid.
4) Line mode: similar The quasi-travel method corrects the shortcomings of the quasi-travel method. The newer Telnet program supports this method.
4. What are the functions and meanings of the SUPPRESSGOAHEAD and ECHO options?
Answer: If the "GOAHEAD" option is activated, it is a half-duplex mode. In order to work in "one character at a time", you need to suppress this option, that is, activate" The SUPPRESSGOAHEAD".ECHO option makes the echo function effective.
When both are activated at the same time, it means that the "one character at a time" work mode is adopted.
5. Why sometimes the Telnet connection cannot be successfully established? How to solve it
Answer: If the server is not on port 23, but is waiting for users to connect on other ports, Telnet will fail at this time and the client needs to change the connected port.
p>
In addition, Telnet is a plaintext transfer protocol. For security reasons, many firewalls disable it. If you need to log in remotely, you can set up a firewall to allow Telnet.
6. Telnet is transmitted in plain text, which has security risks. What should I do?
A: Telnet transmits all user content, including user names and passwords, in clear text on the Internet, which poses security risks, so many servers are disabled Telnet service. But sometimes it is necessary to remotely log in to the server for operation. At this time, you can choose the SSH (SecureShell) program with encryption function.
